Jfuscator offers protection to Java applications by obfuscating the code into bytecode language, making it very difficult to reverse engineer, ensuring enhanced cybersecurity and intellectual property safety.
One of the standout features of Jfuscator is its obfuscation capability, it is so efficient that it protects more of your application than any other obfuscator. It knows what is safe to change and what needs to be left alone, while also giving you full control over the obfuscation process.
The String Morphing feature of Jfuscator is particularly noteworthy as it helps morph strings containing sensitive data to a non-string representation, making them unavailable as strings in the constant pool. This feature allows for string decryption to occur in different parts of the protected application, effectively making an attack based on targeting encrypted strings impossible.
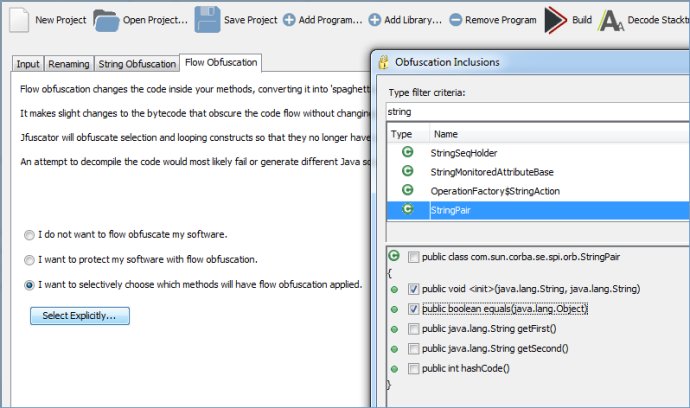
Another great feature of Jfuscator is its Smart Flow Obfuscation that breaks down high-level constructs like loops, conditional and branching instructions by applying code transformations at the bytecode level. This feature obscures program flow without changing what the code does at runtime, ensuring utmost security.
Jfuscator is highly configurable, allowing exclusion of classes, methods, and fields declared in your application, ensuring seamless avoidance of renaming of unwanted classes, methods or fields. It supports all JDKs from 1.1 up to and including Java 7, and can be integrated with your build scripts as a Java-based task.
Other notable features of Jfuscator include stripping debug information by removing source code line numbers, document URLs, and names and types of local variables. It can also protect any type of archive used to deploy your application, including JAR, ZIP, War, and Ear file archives. The Cross-class Renaming feature is also available.
In conclusion, Jfuscator is a valuable tool to safeguard your intellectual property and reduce the risk of your Java applications getting reverse-engineered. It combines efficiency with flexibility to offer a comprehensive obfuscation solution for your Java applications.
Version 2.4: N/A