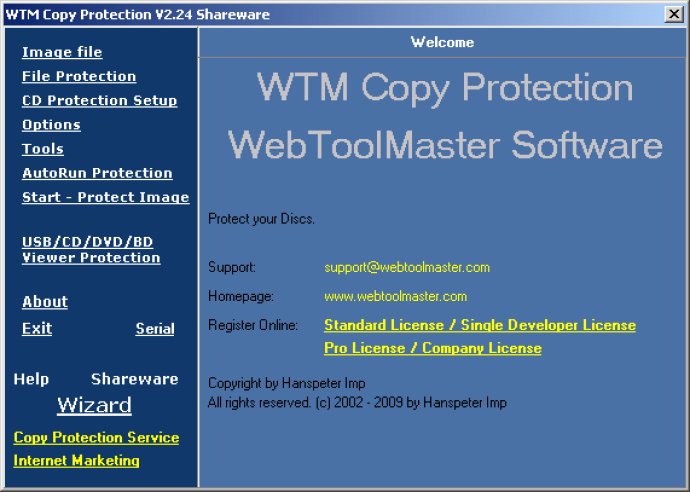
WTM CD Protect is a software solution that ensures protection against illegal copying of software and reduces piracy. It helps businesses earn more profit by preventing unauthorized duplication.
In addition, USB Flash Drive Duplicate Indorsement is a critical and effective feature in safeguarding sensitive information. It allows users to create and encrypt all types of data, including pdf, doc, xls, txt, pps, psd, xml, exe, scr, and more. With USB Flash Drive Text Security, users can protect their digital rights and assets using a USB device key. It is an efficient tool that provides the perfect balance between ease of use and data protection.
Furthermore, CD copy protection, DVD protection, and content protection are significant concerns, and it is essential to have reliable safeguards in place. Apart from legal compliance, it prevents illegal and fraudulent copying, distribution, or use of personal data or business information. DVD Protection with File Protection Mode is a user-friendly tool that ensures that sensitive data remains confidential by encrypting it using powerful coding technology. This feature is designed to provide effective and reliable protection to DVDs.
In conclusion, the WTM software offers top-of-the-line features and capabilities that provide an all-inclusive data security and protection solution. It is ideal for professionals and individuals who wish to safeguard their digital rights and assets, create electronic backups of sensitive data, or protect their financial, personal, or business information from unauthorized access or distribution.
Version 2.71: none.